Every Intel Chip Sold Since 2015 Can Be Hacked To Steal Data; Worst Part? They Cannot Be Fixed Anymore!
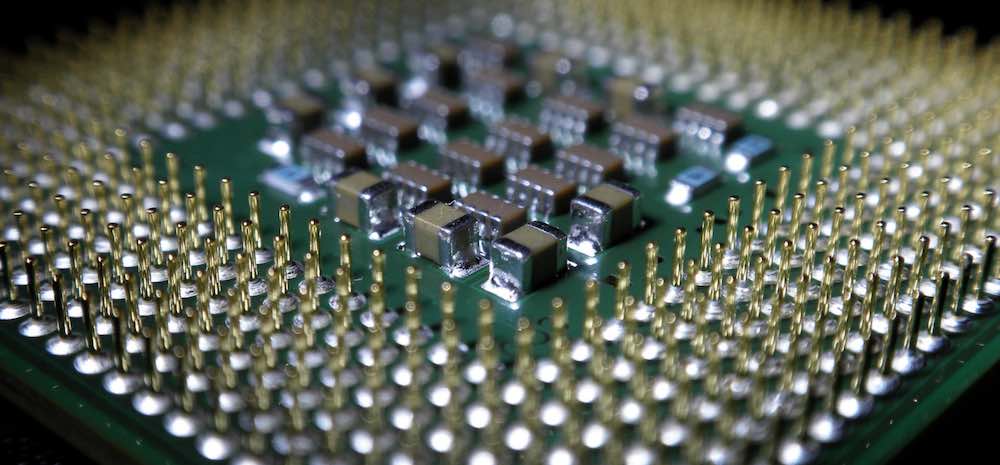
Recently a flaw is discovered in Intel’s chips that opens encrypted data to hackers.
Basically, the security flaw in the Intel chips, that power most desktop and laptop PCs could potentially allow a hacker to decrypt sensitive data.
Not even systems with multiple layers of security can thwart such a hack.
Contents
How Does It Work?
On Thursday, researchers at Positive Technologies disclosed this vulnerability.
According to them, the flaw is an error in the read-only memory (ROM) of Intel microprocessors.
Further, it could allow someone with physical access to a PC to extract its chipset key, essentially a master password that could unlock the rest of the system.
Which Systems Are Affected By This Flaw?
Basically, this flaw affects all PCs with ninth-generation or earlier Intel chips.
Since at least May 2019, Intel has known about the flaw and its latest tenth-generation chips include an updated Converged Security and Management Engine (CSME) unaffected by these ROM errors.
What About The Fix?
The company has also released software and firmware updates to mitigate the problem for affected systems.
But according to the Positive Technologies, the flaws cannot be fixed even with these mitigations, and that the only way to fully prevent an attack is to replace the CPU with a new one whose chipset key cannot be extracted.
The Positive Technologies researcher Mark Ermolov wrote “The problem is not only that it is impossible to fix firmware errors that are hard-coded in the Mask ROM of microprocessors and chipsets,” in a blog post.
“The larger worry is that, because this vulnerability allows a compromise at the hardware level, it destroys the chain of trust for the platform as a whole,” he added.
What Does Intel say?
Intel acknowledged that some of the firmware in its chips are vulnerable to physical attacks and recommended that users “maintain physical possession of their platform,” in a security bulletin updates.
Why This Flaw Makes System So Vulnerable?
As the ROM error can be exploited before a system even boots up, it can’t be patched with a software update, according to Positive Technologies.
Also, this flaw can’t be avoided with some types of added security that are common in business PCs used in finance, healthcare, and other industries.
Typically, those PCs have a trusted platform module (TPM), which prevents hackers from tampering with the system before it boots up.
But CSME firmware also controls software-based TPMs, they are also vulnerable.

Comments are closed, but trackbacks and pingbacks are open.