SBI Warning: Your Mobile Can Be Hacked At Public Charging Stations; How To Avoid ‘Juice Jacking’?
Everyday, we get to hear different incidents of online hacking or invasion of privacy. The truth is with the advancement of technology, hackers and their hacking techniques are getting more and more sophisticated.
We are here today to warn you about a technique commonly referred to as ‘juice jacking’, among hackers and security experts. Trust us, you need to be aware of this situation, now more than ever, thanks to the Holdiay season.
Have You Been Charging your Phones on Charging Stations?
A few days ago, State Bank of India (SBI), the country’s largest lender warned it customers about not using public stations for charging their gadgets, like mobile phones, tabs, laptops or any of their electronic devices holding any form of information that could be misused if hacked.
This being said, SBI also tweeted, warning everyone to think twice before plugging in their electronic devices at charging stations. Malware could find a way in and infect your phones, giving hackers a chance to steal your passwords and export your data.
This is pretty basic right? I mean with the heavy disruption of technology and its diverging forms used for different purposes, its pretty easy to believe that charging from an unreliable source could lead to access of data to an unknown source, given the decree of such incidents.
Public mobile charging stations are common in crowded places. Telecom operators in India also provide charging stations for mobile handsets. The ones with low battery on their phones find these stations useful and happily plug in their mobile for charging. However, it may not be as safe and secure as it appears.
What is Juice Jacking?
Let’s learn a bit more upon the sensitivity of such situations. There is a possible hacking through hardware, most of which makes use of Universal Serial Bus (USB). Since the holiday season is upon us and many more will be travelling, we took this platform to inform you about this form of hacking, not many know.
Juice jacking involves a charging port that can be used as a data connection device as well, typically over USB. With the help of this, hackers either install malware or copy sensitive data from a smartphone, tablet or other computer devices, without the owner’s knowledge. Juice jacking involves a charging port that can be used as a data connection device as well, typically over USB.
Security experts have been warning users about it since many years. The US National Security Agency, in late-2012 warned people to use only their personal power charging cables and not indulge into using public kiosk or charge devices through other people’s computers especially while travelling.
How To Prevent Juice Jacking?
In an attempt to show how such a technique can so easily be put into use, some security researchers and students from Georgia Institute of Technology demonstrated how juice jacking works, in 2013.
Using simple and inexpensive hardware components, they constructed a small-sized wall-charger that could infect an iPhone through malicious software.
There are however, certain precautionary measures that one can take, in order to protect themselves from at least such type of hacking procedure.
- Users should not connect their gadgets to any unknown USB drives.
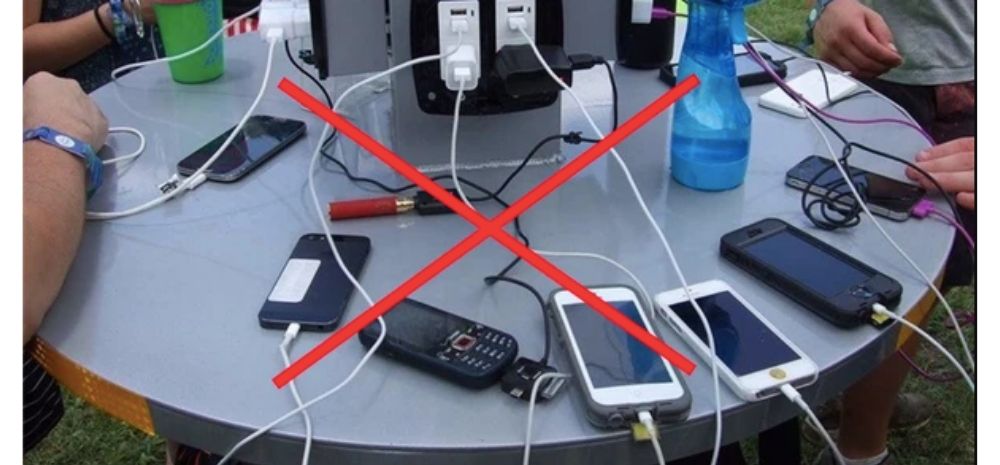
- Never use a public charging station or anyone else’s laptop or PC for charging your electronic devices.
- Make sure to use only your charger and cable provided by the manufacturer of the device.
- Buy a good-quality power bank with sufficient capacity, in case you run out of power.

Comments are closed, but trackbacks and pingbacks are open.