Your OTP Is Hacked! Fraudsters Redirecting Your OTPs, SMSes To Hack Your Phone Using Rs 1200 Tool
Hacking an electronic device, especially a cell phone, has never been very difficult and scammers are always coming up with new ways to exploit the shortcomings of a cellphone.
A new attack has been discovered where SMSes that are being sent to the recipient can be redirected to the scammer’s systems.
Read on to find out how this malware works.
New Attack On Cell Phones: SMSes Redirected To Hackers
This attack was discovered by Motherboard reporter Joseph Cox who had a hacker carry out the same attack on his personal number. It was possible to redirect the messages meant for Cox to arrive on the hacker’s phone and intercept data as well.
And if that wasn’t enough, Cox would also not know that an attack has been conducted and his SMSes are no longer reaching him. Hackers use text-messaging management services that are meant for business and carry out the attack with the help of the exploits in these services.
This also means that these attacks are partially the result of the negligence of the telecom industry, at least in the US.
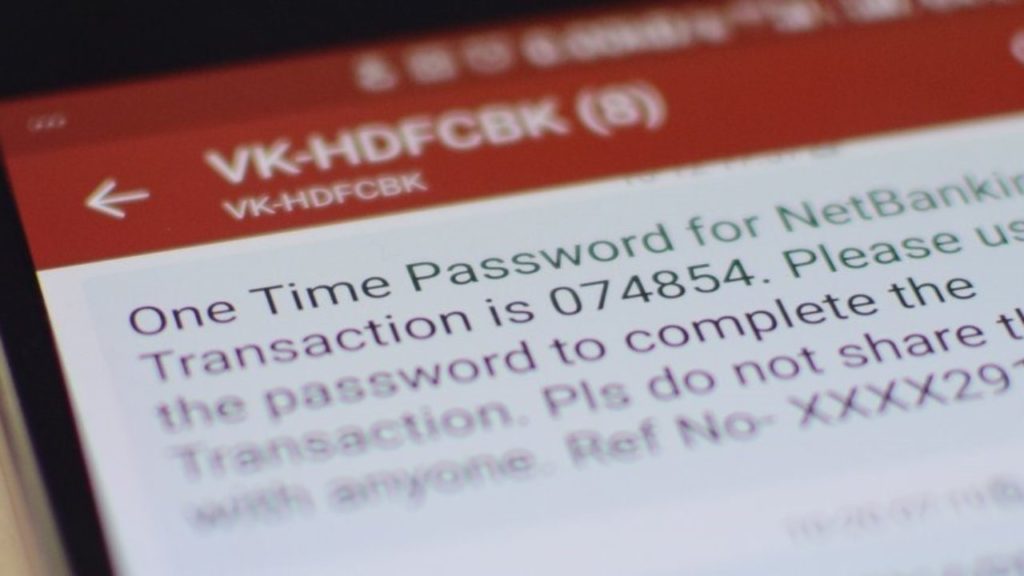
Messages including OTP (one time passwords) or login links for services such as Whatsapp can also be redirected to hackers.
Hackers Using The Exploit With The Help Of Telecom Industry?
The exploit in the services that are responsible is quite big, so much so that the companies that are offering these services are not sending any SMSes to the number that is being attacked to ask permission or even inform the owner that the texts are being forwarded.
The loophole is quite strong and hackers are freely using it with the help of the telecom industry.
As per reports, the hackers are able to access the services by paying only $16 (roughly Rs 1,160). This is a normal fee that providers are given for the SMS redirection services that are meant for paying businesses and not hackers.
In the case of Cox, the company that provided these services has announced that they have fixed the exploit, but there still are multiple others who haven’t. Additionally, some of these companies already have an idea about the exploit and blame CTIA, which is the trade organization for the wireless industry in the US.

Comments are closed, but trackbacks and pingbacks are open.